Penetration Testing Services
Aptive are a UK penetration testing company providing internal and external web & network pen testing services. Our manual pen testing helps with compliance standards such as PCI DSS & ISO 27001.
Aptive are a UK penetration testing company providing internal and external web & network pen testing services. Our manual pen testing helps with compliance standards such as PCI DSS & ISO 27001.
The following section outlines the manual penetration testing services offered by Aptive, which are tailored to the specific needs of UK businesses and organisations. Our cybersecurity experts possess extensive experience in addressing the distinctive security requirements of UK organisations. By employing industry-standard testing methodologies and tools, we are able to identify vulnerabilities, prioritise risks, and provide actionable recommendations to proactively identify potential security risks within your organisation.
Penetration Testing Services:
A network infrastructure penetration test is performed externally or internally to identify vulnerabilities and security issues at the infrastructure level. After discovery, vulnerabilities are safely exploited, confirming if the vulnerability exists. The process is manual, removing false positives typically returned by automated tools and vulnerability assessments.
Web application penetration testing is a method of simulating a real-world attack in order to identify security issues within an organisation’s web applications or web services, such as REST API’s. The identified vulnerabilities are documented in a severity-ordered report, which includes clear recommendation instructions, allowing the organisation to fix and secure the identified security issues..
Mobile app penetration testing is a manual assessment conducted by our consultants against a mobile application. The assessment is typically dynamic, conducted while the application is running, although the client may opt to make the source code available for the assessment. Providing source code optimises testing time by allowing for faster discovery and validation of security vulnerabilities, and removes the need to reverse engineer binaries.
Internal network penetration testing is conducted on-site or via the deployment of an appliance, which enables our team to connect remotely. The deployment of an appliance on-site affords penetration testers the flexibility to perform work outside of normal business hours, thereby reducing costs and the risk of business disruption.
The identification of cybersecurity issues and risks is a crucial aspect of any organisation’s IT security strategy. A comprehensive overview of the current state of IT security is essential for any organisation seeking to evaluate its compliance with various standards, such as PCI DSS and ISO 27001. A certified consultant can provide invaluable assistance in this process, verifying the presence of identified security issues and offering a practical overview of the current state of IT security.
Request a penetration testing quote today
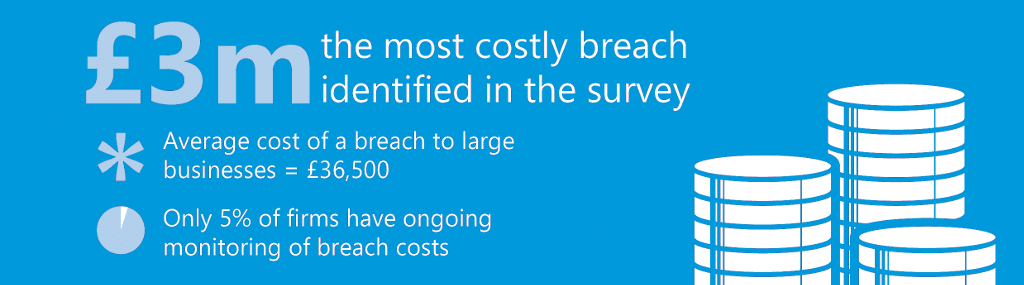
Cyber Security Breaches Survey 2017 – GOV.UK
Cyber Security Breaches Survey 2017 – GOV.UK
Cyber Security Breaches Survey 2017 – GOV.UK
Cyber Security Breaches Survey 2017 – GOV.UK
Assessments should be performed on a regular basis to ensure newly discovered threats and vulnerabilities are discovered and resolved before any potential attacker detects and exploits them in a real world scenario. In addition to regular security assessments demanded by regulatory and compliance standards, network security audits should also be completed when:
Below is an overview of Aptive’s testing process.
Discovery takes place before any engagement is conducted, the process involves collecting as much information about the organisation or application as possible.
In scope addresses are manually enumerated for useful information such as services and versions.
As much information as possible is gathered / enumerated from each exposed service.
After enumeration of the server(s) / network a Vulnerability assessment is completed, helping identify known public vulnerabilities. This process helps identify information that can be manually assessed in the next step.
Depending on client requirements, discovered forms or password hashes are tested using the latest password recovery techniques, helping identify if current password policies are sufficient.
Services revealed at the enumeration and vulnerability assessment stage are researched for public exploits and or known exploit methods.
Discovered services are manually and safely tested or exploited to confirm if they are vulnerable.
Successfully compromised machines are locally enumerated for valuable data, if possible (scope permitting) user privileges are escalated to admin root. Screenshots of account privilege level or discovered data are taken for evidence.
Lateral movement uses compromised machines are used to route traffic, allowing the pen testing consultant to access the internal network or other machines / network subnet. This demonstrates the risk of a potential breach and how far an attacker may get within the target companies network.
All discovered security findings are documented in severity ordered report with clear concise remediation instructions and their associated risk and impact.
All our manual assessment services come with free retesting on reported findings.
All our penetration testing services are performed manually using methodologies based on industry-approved frameworks such as OWASP. If you would like to sample the quality of our work you can request an example report.
| Type | Starting Price | Description |
|---|---|---|
| External Network | Request Price | Price for an external test for up to 10 external IP addresses, pen testing assesses an organisations network & infrastructure externally, helping identify vulnerabilities & security issues. |
| Internal Network | Request Price | Price for internal test for up to 25 internal addresses, pen testing is performed inside the corporate network, assessing operating system & infrastructure security vulnerabilities. * |
| Web Application | Request Price | Price for a manual security assessment of a single web application consisting of less than 25 static or dynamic pages, 1 level of authentication. The web app security test includes file upload testing and all areas of the OWASP top 10. |
| Mobile Application | Request Price | Price for a manual mobile app security assessment for a single iOS or Android application, mobile apps are assessed using a methodology based on the OWASP mobile testing framework. |
| Wireless | Request Price | Wireless network security audit, performed manually. Price is for a single AP as part of an internal pen test, additional AP's can be added for an additional charge. |